Over the past few weeks, WordFence have reported an active attack targeting a selection of new and old WordPress Plugin Vulnerabilities. these attacks see to maliciously redirect traffic from victims website to a number of potentially harmful locations.
Today we assisted a company that was a target of this Malicious Redirect Campain. It shows while you think it might not happen to you, the chances are still quite high. They are not targetting ‘you’ they are just trying to scan the web for loop holds to add their redirects. This particular case redirected ALL links to another website, including the backend login link.
Current Plugins that have been targeted:
- NicDark Plugins – Unauthenticated Arbitrary Options Update
- Though several individual plugins are affected, the vulnerability is the same across each and they are covered by a single firewall rule.
- Affected plugin slugs are prefixed with
nd-. Example plugins include Components For WP Bakery Page Builder (slug:nd-shortcodes), Booking (slug:nd-booking), Travel Management (slug:nd-travel), etc. - Firewall rule released for Premium users on July 30, 2019
- Available for Free users starting August 29. 2019
- Simple 301 Redirects Addon – Bulk Uploader <= 1.2.5 – Unauthenticated Options Update
- Firewall rule released for Premium users on August 6, 2019
- Available for Free users starting September 5, 2019
- Bold Page Builder
- Blog Designer
- Live Chat with Facebook Messenger
- Yuzo Related Posts
- Visual CSS Style Editor
- WP Live Chat Support
- Form Lightbox
- Hybrid Composer
- WP Private Content Plus
- WP Mail SMTP by WPForms
- All former NicDark plugins (nd-booking, nd-travel, nd-learning, et. al.)
A list of IP addresses you should block if you are using free security software (or premium)
IP address causing most of the issues: 104.130.139.134 Additional IP addresses to block:- 192.99.38.186
- 51.38.69.87
- 62.210.252.196
- 164.132.44.97
- 159.203.81.46
- 217.182.95.250
- 51.255.43.81
- 37.187.198.246
- 54.36.246.232
- 45.55.152.56
- 198.199.100.240
- 162.241.175.243
- 188.213.175.168
- 45.40.143.13
- 188.213.166.219
- 192.169.227.95
- 193.70.2.138
- 149.202.75.164
- 192.169.157.142
- 104.238.97.201
What can you do to minimise the chances of an attack?
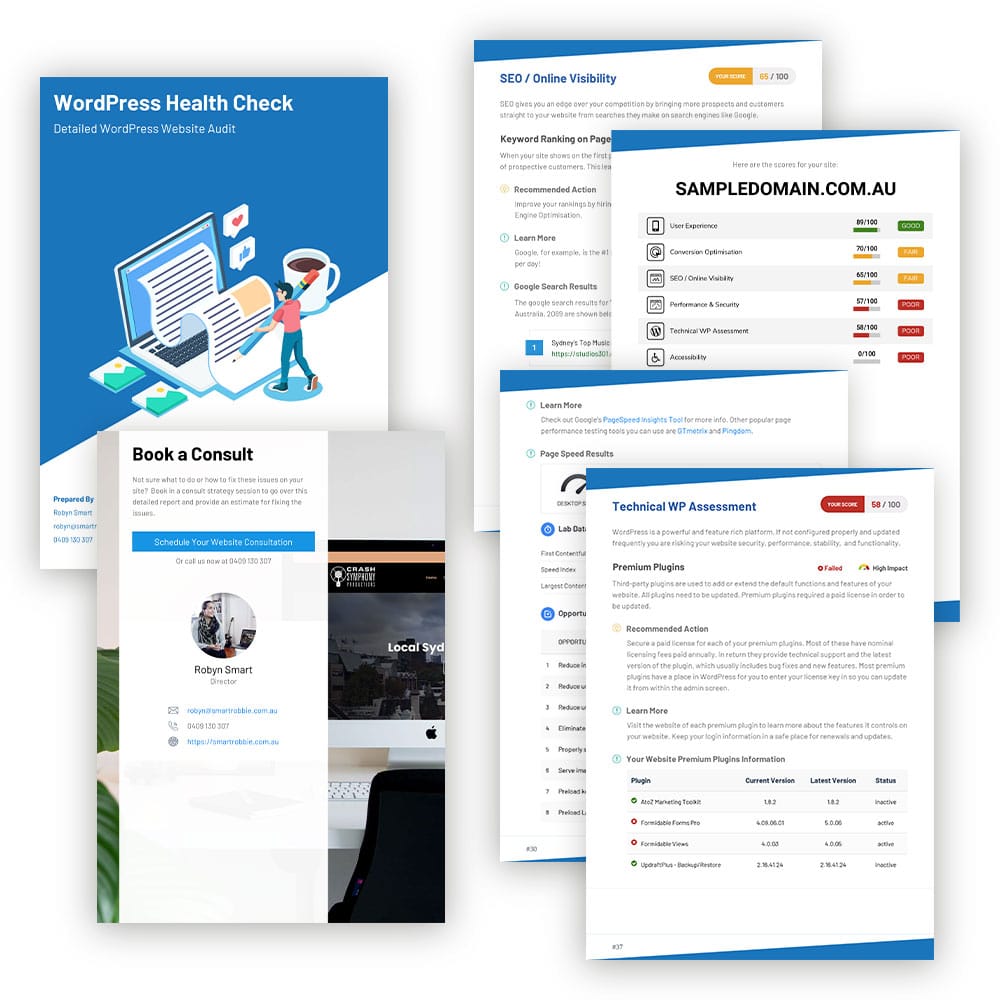
1. Keep your website up to date – Theme Files, Plugins and WordPress versions. We recommend you do this weekly or at a minimum once a month. If you need assistance with this so you don’t have to worrk about it, we have website care plans available: Smartrobbie 2. Set up a Sucuri Firewall – Sucuri is a great service. They can your site every 12 hours for any malware and send reports. They also have a firewall which blocks out any potential hacking. You can set the firewall to only allow backend access to approved IP addresses. Prices start at $199/year US – Sucuri. It’s a highly recommended service which we use in the event of any hacks. They are very efficient, remove the hack quickly and continue to monitor the site for the life of the plan. If you are hacked, get an account today and they will fix it for you. Set up a free trial Sucuri firewall here:Free Trial Firewall
3. WordFence Premium – Are you using the Free version of WordFence? We highly recommend upgrading to the Premium version:- Receive real-time Firewall and Scan engine rule updates for protection as threats emerge
- Real-time IP Blacklist blocks the most malicious IPs from accessing your site
- Country blocking
- IP reputation monitoring
- Schedule scans to run more frequently and at optimal times
- Access to Premium Support
- Discounts for multi-year and multi-license purchases